- You are here:
-
Blog

-
Michael Van Der Klei (RHCE/ICBB)

- Businesses are Feeling the Impact of Supply Chain Issues
Aniar Blog
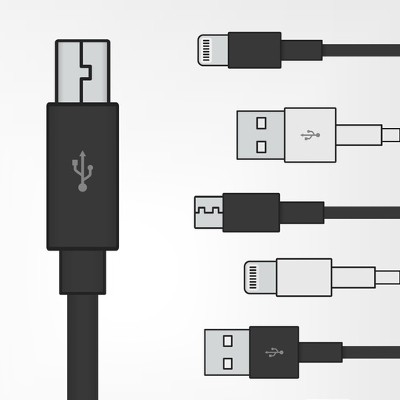
Can Chargers Be Interchanged Between Devices?
One of the major benefits of a laptop is the mobility that it permits--but this is a double-edged sword, as this mobility means that you are relying on the device’s battery life. Of course, if your laptop begins to die, you can always borrow someone else’s charger, right?
Actually, this is a very bad idea, as it puts your device at serious risk. There are a few reasons why this is the case.
Manufacturer Differences
When whichever company produced your laptop did so, it did so in a very specific way. This includes the charger that comes with the laptop. Trying a different manufacturer’s charger with your laptop will almost certainly damage your battery. Best case scenario, your laptop’s battery will reject the charger. You should only ever use a charger that was produced by the device’s manufacturer, even if another charger appears to supply the same amount of power.
On the subject of power…
Different Power Requirements
Like we mentioned before, your laptop’s original charger was specifically manufactured to your laptop’s specifications. As a result, the charger is made to supply exactly how much power your device needs. A charger from a different manufacturer might supply too much or too little power, potentially damaging the battery or the laptop’s other hardware.
Why You Should Avoid Cheap Off-Brand Chargers
If it’s bad to utilize another established brand’s charger, it’s worse to subject your laptop to a knock-off, no-name charger. There is no guarantee that the charger is of a trustworthy quality, as well as no way to tell if its alleged power output is actually what it sends into your device. If you do need to replace your charger, or you just want a spare, invest in the real McCoy. Otherwise, your short-term costs savings may translate into the cost of a new device.
Have you ever found yourself without a charger and tempted to borrow someone else’s? What happened if and when your battery died? Share your experience with us in the comments!
About the author
Michael is the CTO at Aniar IT Services and has been working in IT for over 20 years.
Mobile? Grab this Article!
Tag Cloud
Comments